Documentation Index
Fetch the complete documentation index at: https://cosmos-docs-evm-upgrade-7.mintlify.app/llms.txt
Use this file to discover all available pages before exploring further.
Synopsis
This standards document describes the abstraction of an IBC connection: two stateful objects (connection ends) on two separate chains, each associated with a light client of the other chain, which together facilitate cross-chain sub-state verification and packet association (through channels). A protocol for safely establishing a connection between two chains is described.Motivation
The core IBC protocol provides authorisation and ordering semantics for packets: guarantees, respectively, that packets have been committed on the sending blockchain (and according state transitions executed, such as escrowing tokens), and that they have been committed exactly once in a particular order and can be delivered exactly once in that same order. The connection abstraction specified in this standard, in conjunction with the client abstraction specified in ICS 2, defines the authorisation semantics of IBC. Ordering semantics are described in ICS 4).Definitions
Client-related types & functions are as defined in ICS 2. Channel and packet-related functions are as defined in ICS 4. Commitment proof related types & functions are defined in ICS 23Identifier and other host state machine requirements are as defined in ICS 24. The identifier is not necessarily intended to be a human-readable name (and likely should not be, to discourage squatting or racing for identifiers).
The opening handshake protocol allows each chain to verify the identifier used to reference the connection on the other chain, enabling modules on each chain to reason about the reference on the other chain.
An actor, as referred to in this specification, is an entity capable of executing datagrams who is paying for computation / storage (via gas or a similar mechanism) but is otherwise untrusted. Possible actors include:
- End users signing with an account key
- On-chain smart contracts acting autonomously or in response to another transaction
- On-chain modules acting in response to another transaction or in a scheduled manner
Desired Properties
- Implementing blockchains should be able to safely allow untrusted actors to open and update connections.
Pre-Establishment
Prior to connection establishment:- No further IBC sub-protocols should operate, since cross-chain sub-states cannot be verified.
- The initiating actor (who creates the connection) must be able to specify an initial consensus state for the chain to connect to and an initial consensus state for the connecting chain (implicitly, e.g. by sending the transaction).
During Handshake
Once a negotiation handshake has begun:- Only the appropriate handshake datagrams can be executed in order.
- No third chain can masquerade as one of the two handshaking chains
Post-Establishment
Once a negotiation handshake has completed:- The created connection objects on both chains contain the consensus states specified by the initiating actor.
- No other connection objects can be maliciously created on other chains by replaying datagrams.
Technical Specification
Data Structures
This ICS defines theConnectionState and ConnectionEnd types:
- The
statefield describes the current state of the connection end. - The
counterpartyConnectionIdentifierfield identifies the connection end on the counterparty chain associated with this connection. - The
counterpartyPrefixfield contains the prefix used for state verification on the counterparty chain associated with this connection. Chains should expose an endpoint to allow relayers to query the connection prefix. If not specified, a defaultcounterpartyPrefixof"ibc"should be used. - The
clientIdentifierfield identifies the client associated with this connection. - The
counterpartyClientIdentifierfield identifies the client on the counterparty chain associated with this connection. - The
versionfield is an opaque string which can be utilised to determine encodings or protocols for channels or packets utilising this connection. If not specified, a defaultversionof""should be used. - The
delayPeriodTimeindicates a period in time that must elapse after validation of a header before a packet, acknowledgement, proof of receipt, or timeout can be processed. - The
delayPeriodBlocksindicates a period in blocks that must elapse after validation of a header before a packet, acknowledgement, proof of receipt, or timeout can be processed.
Store paths
Connection paths are stored under a unique identifier.Helper functions
addConnectionToClient is used to add a connection identifier to the set of connections associated with a client.
CommitmentPrefix associated with the connection to the verification function
provided by the client. In the other parts of the specifications, these functions MUST be used for introspecting other chains’ state,
instead of directly calling the verification functions on the client.
Sub-protocols
This ICS defines the opening handshake subprotocol. Once opened, connections cannot be closed and identifiers cannot be reallocated (this prevents packet replay or authorisation confusion). Header tracking and misbehaviour detection are defined in ICS 2.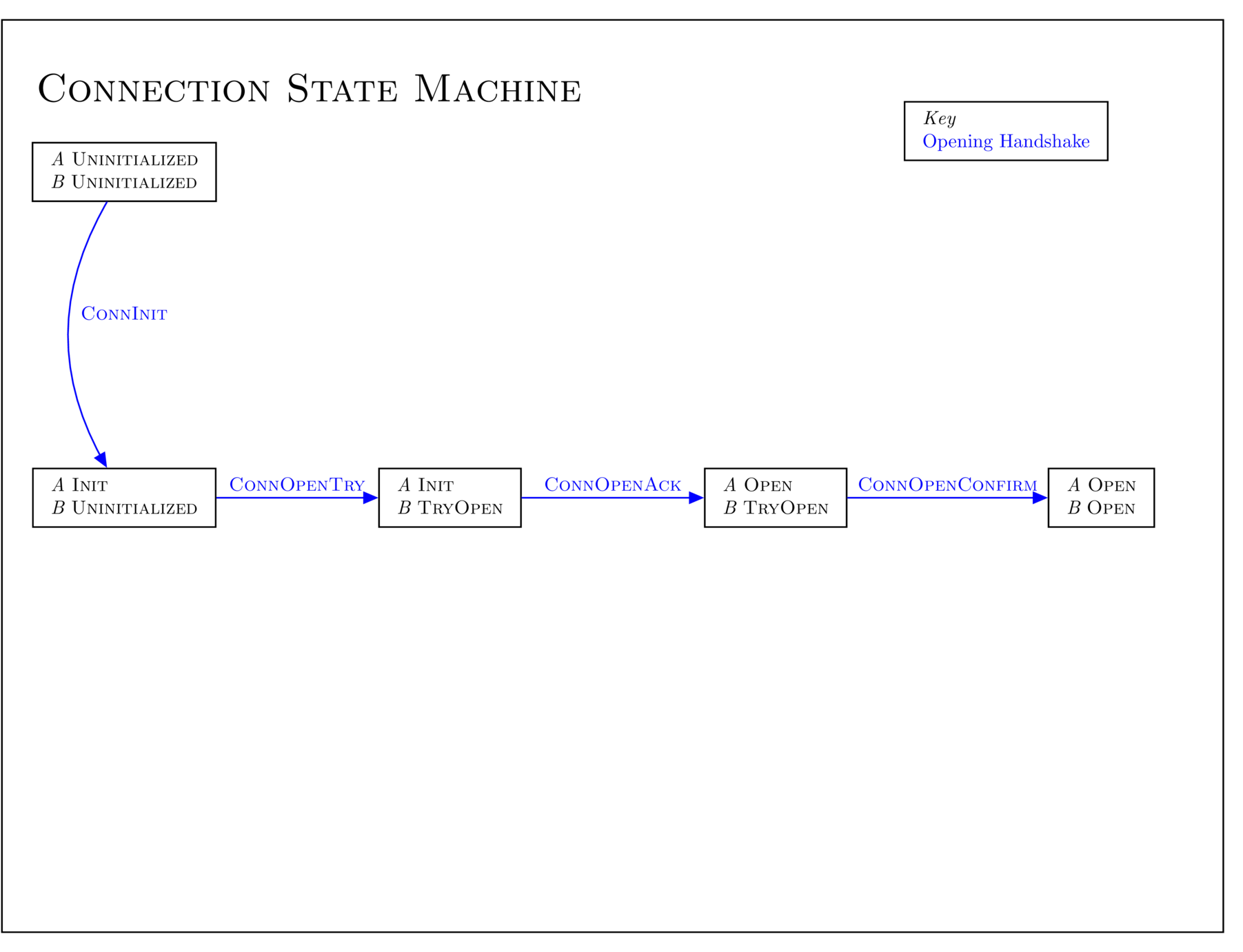
Identifier validation
Connections are stored under a uniqueIdentifier prefix.
The validation function validateConnectionIdentifier MAY be provided.
validateConnectionIdentifier function will always return true.
Versioning
During the handshake process, two ends of a connection come to agreement on a version associated with that connection. ThisVersion datatype is defined as:
identifier field specifies a unique version identifier. A value of "1"
specifies IBC 1.0.0.
The features field specifies a list of features compatible with the specified
identifier. The values "ORDER_UNORDERED" and "ORDER_ORDERED" specify
unordered and ordered channels, respectively.
Host state machine MUST utilise the version data to negotiate encodings,
priorities, or connection-specific metadata related to custom logic on top of
IBC. It is assumed that the two chains running the opening handshake have at
least one compatible version in common (i.e., the compatible versions of the two
chains must have a non-empty intersection). If the two chains do not have any
mutually acceptable versions, the handshake will fail.
An implementation MUST define a function getCompatibleVersions which returns the list of versions it supports, ranked by descending preference order.
pickVersion to choose a version from a list of versions.
Opening Handshake
The opening handshake sub-protocol serves to initialise consensus states for two chains on each other. The opening handshake defines four datagrams: ConnOpenInit, ConnOpenTry, ConnOpenAck, and ConnOpenConfirm. A correct protocol execution flows as follows (note that all calls are made through modules per ICS 25):| Initiator | Datagram | Chain acted upon | Prior state (A, B) | Posterior state (A, B) |
|---|---|---|---|---|
| Actor | ConnOpenInit | A | (none, none) | (INIT, none) |
| Relayer | ConnOpenTry | B | (INIT, none) | (INIT, TRYOPEN) |
| Relayer | ConnOpenAck | A | (INIT, TRYOPEN) | (OPEN, TRYOPEN) |
| Relayer | ConnOpenConfirm | B | (OPEN, TRYOPEN) | (OPEN, OPEN) |
- Each chain has each other’s correct consensus state as originally specified by the initiating actor.
- Each chain has knowledge of and has agreed to its identifier on the other chain.
generateIdentifier which chooses an identifier, e.g. by incrementing a counter:
version to ensure that the handshake will either complete with that version or fail.
ConnOpenInit initialises a connection attempt on chain A.
Querying
Connections can be queried by identifier withqueryConnection.
queryClientConnections.
Properties & Invariants
- Connection identifiers are first-come-first-serve: once a connection has been negotiated, a unique identifier pair exists between two chains.
- The connection handshake cannot be man-in-the-middled by another blockchain’s IBC handler.
Backwards Compatibility
In the latest specification of the connection handshake,connOpenTry and connOpenAck will no longer validate that the counterparty’s clien state and consensus state is a valid client of the executing chain’s consensus protocol. Thus, clientState, proofClient, proofConsensus and consensusHeight fields in the ConnOpenTry and ConnOpenACk datagrams are deprecated and will eventually be removed.
Forwards Compatibility
A future version of this ICS will include version negotiation in the opening handshake. Once a connection has been established and a version negotiated, future version updates can be negotiated per ICS 6. The consensus state can only be updated as allowed by theupdateConsensusState function defined by the consensus protocol chosen when the connection is established.
Example Implementations
- Implementation of ICS 03 in Go can be found in ibc-go repository.
- Implementation of ICS 03 in Rust can be found in ibc-rs repository.
History
Parts of this document were inspired by the previous IBC specification. Mar 29, 2019 - Initial draft version submitted May 17, 2019 - Draft finalised Jul 29, 2019 - Revisions to track connection set associated with client Jul 27, 2022 - Addition ofClientState validation in connOpenTry and connOpenAck
Jul 23, 2024 - Removal of ClientState and ConsensusState validation in connOpenTry and connOpenAck. For information on the consequences of these changes see the attached diagram and consequences document